Note*: To install & run the tools mentioned in this blog, check my blog in the above video description.
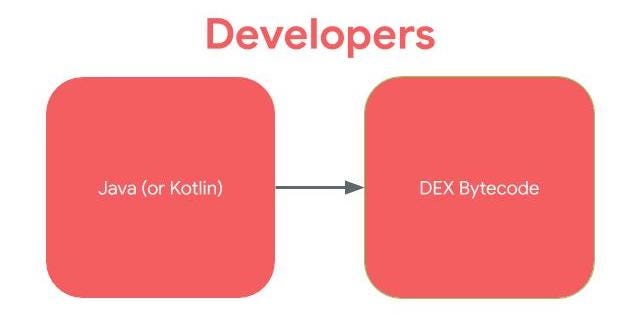
Most Android applications are written in Java. Instead of the Java code being run in Java Virtual Machine (JVM) like desktop applications, in Android, the Java is compiled to the Dalvik Executable (DEX) bytecode format. For more recent versions of Android, the Android Runtime (ART) is used.
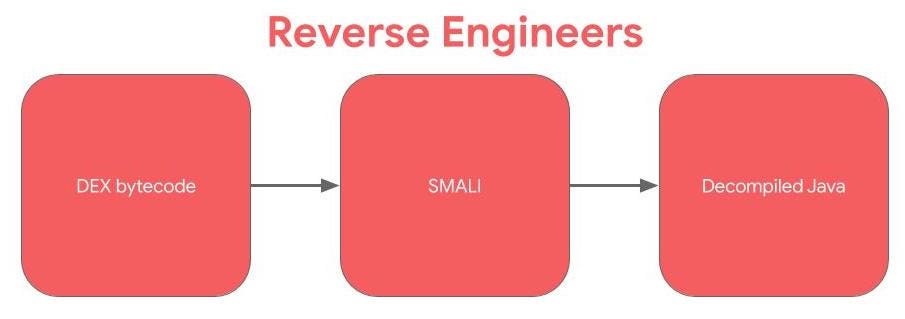
Smali is the human readable version of Dalvik bytecode. SMALI is like the assembly language. Smali Instruction set.
To get the Smali from DEX, you can use the baksmali tool (disassembler)
Check List:
1. Run apkleaks to find leaked credentials, and validate the credentials using nuclei token-spray.
2. Use apktool to reverse-engineer the apk. And check the following things:
3. Check: /assets and /res/raw
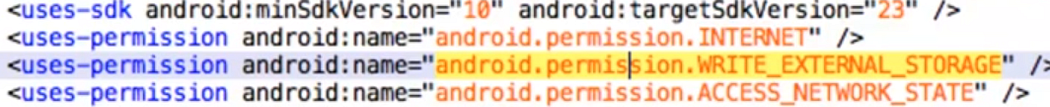
4. Check: Manifest, (it is like the table of contents): for “External storage”, “intents”
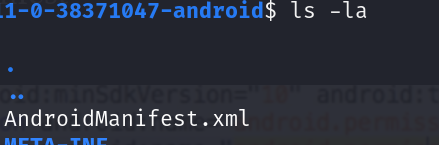
5. Use “ls -a”, to view hidden files when browsing directories.
6. Inotify (inode notify) is a Linux kernel subsystem that monitors file system changes and reports them to applications.
7. Check all the imports.
8. Frida (Dynamic analysis):
allows you to modify, hook, and dynamically interact with applications, hook methods, inspect class variables, and more.
9. dex2jar:
converts .dex files into .jar files. It is relatively easy to decompile a .class and .jar file back to source code.
10. JADX:
apk reverse engineering tool. You can instruct jadx do this by using the “ — deobf” flag in combination with “ — deobf-min”.
Example: ./jadx — deobf — deobf-min 3 …
For example take an app with multiple “a.java” files, and output them as unique class names like “C1234a.java”. As a result, you don’t have to sort through all the different uses of “a.java”, and instead, you can just search for uses of “C1234a.java”.
11. A common decompilation flow looks like this:
- Use apktool to extract APK and decompress resource files
- Use jadx to decompile.
12. aapt dump badging <my_app.apk> :
dump things like the AndroidManifest.xml tree from an APK without needing to decompile or extract anything.13. Proxying Android Over USB:
Here’s how to set it up:
- Make sure your device is connected via ADB
- adb reverse tcp:8080 tcp:8080
- Settings -> WiFi -> Long Press Network -> Manage Network -> Advanced -> Proxy -> Manual
- Proxy Host: 127.0.0.1
- Proxy Port: 8080
- Press Save
Now your device should send all traffic to 127.0.0.1:8080 which is then proxied over USB to port 8080 on your host machine. No more spotty connections or wondering if your router is blocking proxy connections.
14. Logcat is a command-line tool that dumps a log of system messages including messages that you have written from your app with the
Logclass.15. Install genymotion in desktop & do Dynamic analysis of apk in mobsf
Comments
Post a Comment