GitHub: https://github.com/AdithyakrishnaV/RUST-calculator

“mut”: This keyword makes the binding mutable
The “String::new()” function returns a new, empty string
The empty string is being assigned to the binding “n1”
stdout().flush() is used to make sure that the output written to the standard output stream is immediately displayed and not buffered. It’s especially useful when debugging, where the immediate display of output can help in understanding the program’s behavior.
n1.trim(): This method call trims whitespace from the beginning and end of the string stored in n1.
.parse(): This method call attempts to parse the trimmed string into a number.
Another way:
let operations = String::from(“+-*/”);
if !operations.contains(operator){
println!(“Invalid operator”);
return;
}
Rust programming language:
Rust is a modern, systems programming language that is designed for speed, reliability, and security.
Memory Safety and Control: Rust offers memory safety through its ownership model, which helps prevent common programming errors like null or dangling pointer references.
Concurrent Programming: Rust supports concurrent programming through its lightweight “tasks” system, which allows multiple threads to run in parallel.
Strong Standard Library: Rust has a robust standard library that provides a wealth of functionality, making it easier to write code and get things done.
Built-In Testing Framework: Rust has a built-in testing framework, making it simple to write and run tests for your code, ensuring that it works as expected.
Active Community: Rust has a thriving and supportive community, offering a wealth of resources and support for learning and using the language.
Wide Range of Applications: Rust is used in a variety of applications, from web development to operating systems, and is becoming an increasingly popular choice for building high-performance and reliable software
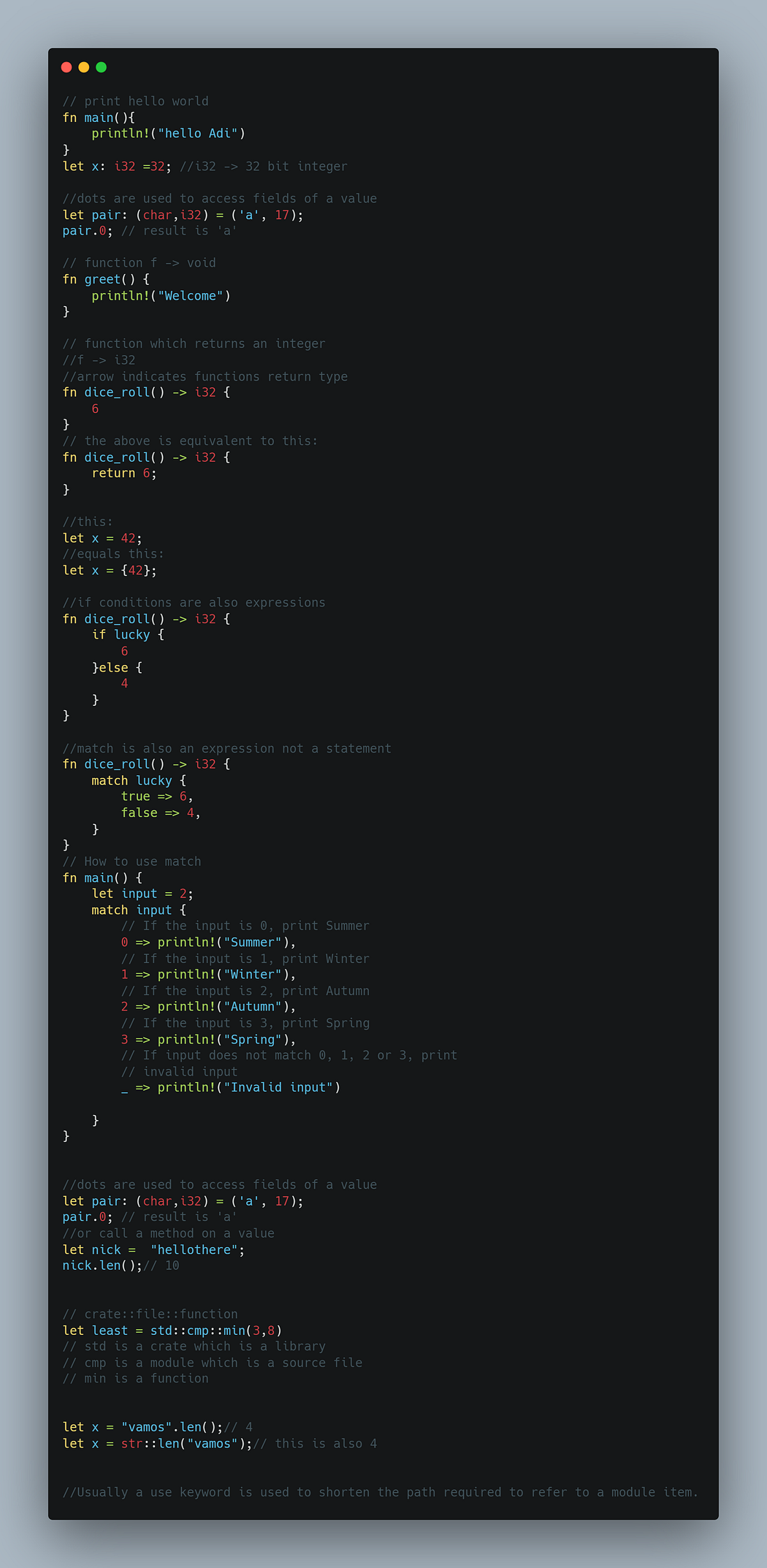
Some basics to get started:
Comments
Post a Comment