hashing is a one-way function. So we cannot reverse the hash we can only Brute-force it and check for a similar hash

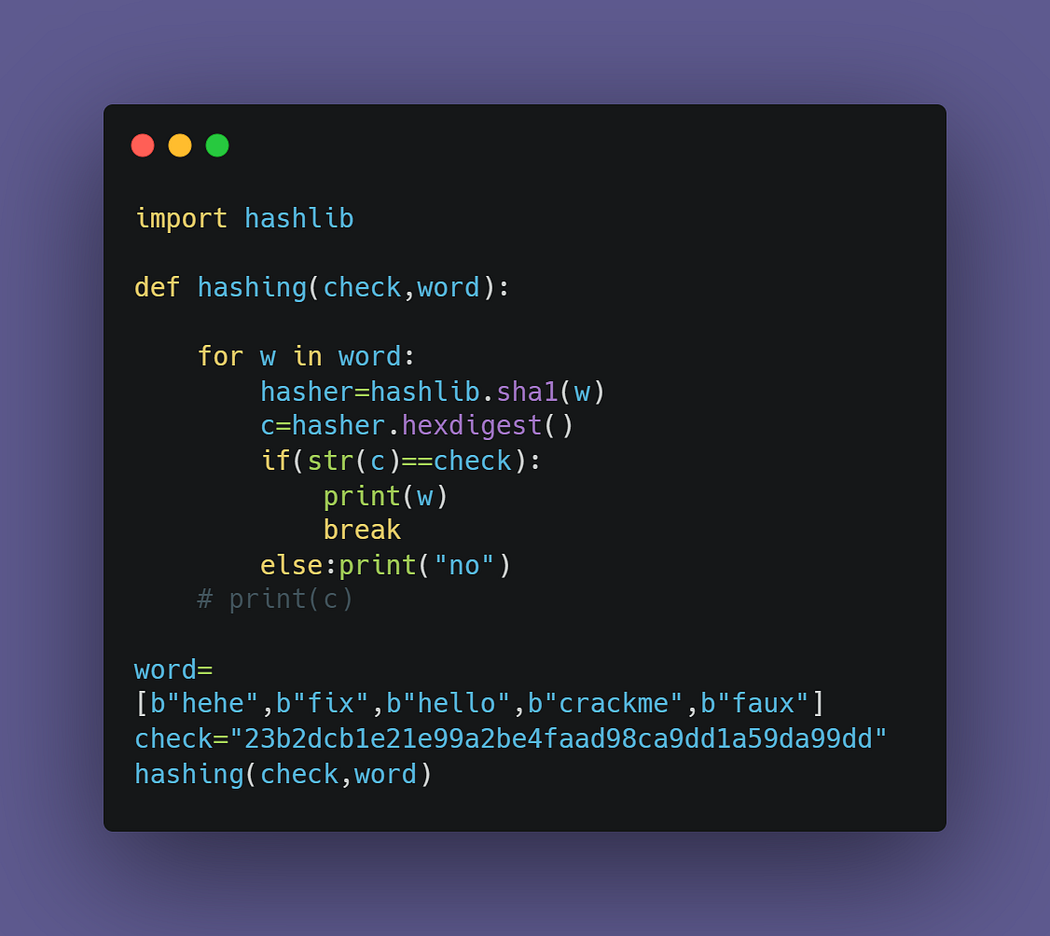
import hashlibThis line imports the hashlib library, which provides implementations of various hash functions.
def hashing(check,word):This line defines a function called hashing that takes two parameters: check and word
for w in word:This line sets up a loop that iterates over each word in the word list.
hasher=hashlib.sha1(w.encode())This line uses the SHA1 algorithm from the hashlib library to hash the current w word in the loop. It first encodes the word as bytes using the encode() method.
c=hasher.hexdigest()This line extracts the resulting hash from the hasher object and converts it to a string of hexadecimal digits using the hexdigest() method.
if(str(c)==check):This line checks whether the resulting hash string matches the check parameter. It converts the hash string to a regular string using str() to ensure the comparison is done correctly.
print("\n"+w+"\n")
breakIf there is a match, this line prints the matching word and breaks out of the loop. The \n characters create a new line before and after the word for better readability.
else:
print("no")If there is no match, this line prints "no".
f= open("pass.txt", "r")
word=f.read().split()This line opens the file pass.txt in read mode, reads its contents into a string, and splits the string into a list of words. The word variable is set to this list.
check=input("Enter the hash: \n ")This line prompts the user to enter a hash to check against.
hashing(check,word)This line calls the hashing function with the check and word parameters.
f.close()This line closes the pass.txt file
Another way:
But this is not fast if we have a big list of words then let’s make it faster the next time may be using RUST
Comments
Post a Comment